More and more companies are using technologies and are constantly expanding them with individual functions that increasingly support processes in companies. The data obtained in this way are often worth protecting and critical for the company. The non-transparent storage of the data therefore creates a risk for companies.
As early as in the coalition agreement, the governing parties commit themselves to preserving and regaining technological sovereignty. The focus is on alternatives to current US providers, which often offer cloud and software solutions without sufficient transparency. Due to the fact that we will become more and more dependent on technologies in the future, the sovereignty over their administration should lie in the hands of the German entrepreneurs.
This article shows current risks in the cooperation with large US providers and explains the use of open source software as an alternative solution for creating digital sovereignty.
Risk 1: Vendor LockIn
The reason for the frequent focus on one provider is obvious: Providers such as Apple and Microsoft often optimize their own components and it is difficult to link them with solutions from other manufacturers. One speaks of a vendor lock-in:
With vendor lock-in, a customer cannot replace a used service or product with an equivalent solution from another provider without increased effort. This is mostly due to the use of proprietary technologies that are incompatible with those of competitors.
Lindner et al. (2020)
The risks of such a vendor lock-in are often high costs and license fees, as there is a strong dependency on the individual provider.
Risk 2: Data in the cloud – but how are you?
Another risk is the storage of the data, which is often in the provider’s cloud. Cloud is defined as:
The term includes the interaction of several servers over the Internet. All servers share tasks among themselves. If one server fails, another server takes over. The cloud user does not have an overview of the individual servers. His data or applications run somehow (cloudy) in the cloud.
Lindner et al. 2020
You notice that the data in the cloud is therefore often not stored transparently and therefore it cannot be 100% guaranteed that the data is adequately protected from third party access. Such storage also often violates order data processing agreements (ADV) with important key customers.

Digital sovereignty
sovereignty is defined as the ability of a natural or legal person to have exclusive self-determination. The ability to self-determination is shaped by the self-reliance and independence of the individual and is the middle way too External control and self-sufficiency.
Delimitation: Sovereignty does not mean that a company has to do everything itself ( Self-sufficiency ) but that a company is able to act and can decide for itself what it does. It is able to choose between alternatives using powerful software.
The Digital sovereignty For me, stands for independence from a provider as well as self-determination as to which components I can use to digitally support a certain activity in the company. Furthermore, I have complete transparency about my data.
In the following I would like to show an example from my current experience for companies as well as private households.
Open source as an alternative for companies
For almost every task there is free, so-called open source software, which often does not have to hide behind commercial applications. Open source software is software whose source code is freely available and can be downloaded from the Internet and used free of charge within the framework of open source license models. By publishing the source code, the user can understand that data is not used without the consent of the user (Lindner at al. 2020).
Let’s take the example of Office 365 from Microsoft, which is used in numerous companies for the following activities:
- Writing program (Word),
- Tables (Excel),
- Presentations (PowerPoint),
- Notes (OneNote),
- Videoconference (Skype),
- Email (Outlook) and
- File sharing (OneDrive).
Microsoft Office 365 combines various online services with classic desktop office software. Office 365 is available in different scope of services. The web applications can be used via a browser on computers with any operating system (Lindner at al. 2020)
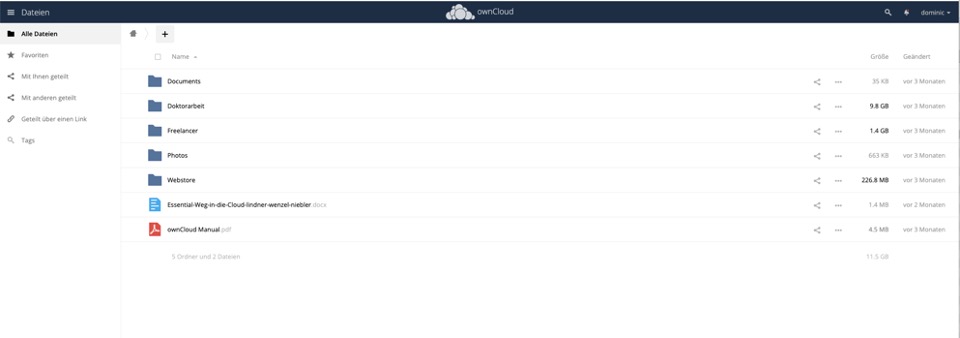
There is also a secure alternative for Office 365. The various services could also be obtained on the basis of open source software. Through e.g. On premise installation (own server or free choice of data center) and a large number of administration and security features, entrepreneurs have full control over their data and are compliant with the GDPR (Lindner at al. 2020). The following figure shows the implementation by ownCloud with Collabora in the browser as an alternative to Microsoft Word and OneDrive.
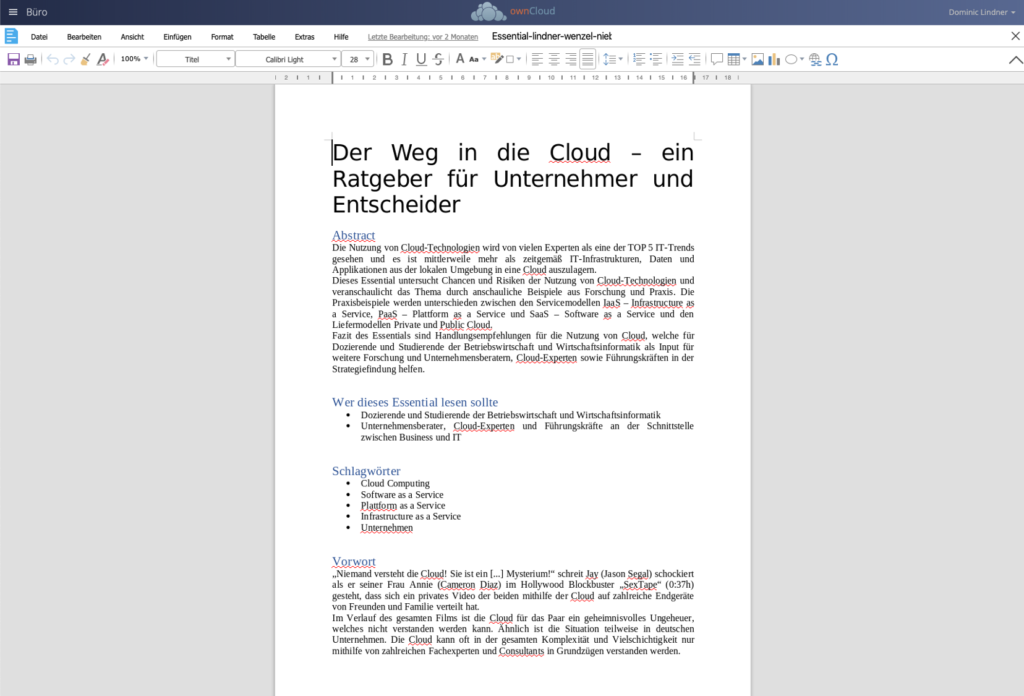
Similarly, the entire functionality of Office 365 can now be recreated using individual open source variants. My advice is:
- Writing program, tables and presentations (OnlyOffice),
- Notes (Joplin),
- Videoconference (Kopano),
- User administration (Univention)
- Email (Open XChange) and
- File sharing (ownCloud).
These functions can be set up flexibly and integrated into the existing open source infrastructure. You can also exchange individual components at any time (no Verdor LockIn) and have transparent source code.
Open source as an alternative for the home
In private, too, you should pay more attention to the sovereignty of your own data. Similar to companies, providers such as Dropbox or Microsoft also give private users little transparency in the storage of their own data.
For example, I connected two hard drives (4TB) to a Raspberry PI at home. The hard drives are redundant so that data loss is not possible if one hard drive fails. The whole set will cost you around 250 euros. Since commercial clouds often cost 10 euros per month, this investment is worthwhile after 2 years. However, this was not my primary goal because I wanted to achieve sovereignty of my data.

I then installed the ownCloud software on my Raspberry PI. Because of the open source end, I could be sure that nobody would have access to my data. I also know exactly that the data is on my hard drives, which are on my desk.
Reading tip: read mine Instructions on how to set up such a cloud !
The alternative is to buy your own NAS station. For example, I still have a Synology NAS. Long established in PC circles, Synology is one of the leading manufacturers of NAS servers. The fully configured version is particularly suitable for beginners and requires very little knowledge. Components can be installed and set up with a click. They are not completely free, however, unlike Dropbox and Co., they have their own hardware. Here is my recommendation: Synology NAS DS-218 with 2 Seagate hard drives .
Conclusion
Digital sovereignty is an essential topic for companies. As more and more technology is being established in companies, the topic should also become more and more important. The main dangers are the dependency on a provider and the associated high costs as well as the lack of transparency of the data.
For almost every task there is free, so-called open source software, which often does not have to hide behind commercial applications. The use of such software can be an alternative to commercial providers and increase the digital sovereignty of companies and private households.
Tip: Read my new book: The way to the cloud at Springer Gabler or book me for a talk .
Image source: Pixabay
source
Lindner, D., Niebler, P., & Wenzel, M. (2020). The way to the cloud – a guide for entrepreneurs and decision-makers . Heidelberg: Springer Gabler.
[werbung] [fotolia]


